Numbers we stand behind —
measured, not marketed.
Intelligence that thinks
ahead of attackers.
The first AI-native threat intelligence platform built for the GCC — correlating billions of signals to predict, prove, and prevent breaches.
Watch the underground. Surface what matters.
Continuous coverage across forums, marketplaces, and infostealer logs — correlated to your assets, leaked credentials, and named executives.
Operators on call,
across every surface.
If it runs on data,
we can put AI on it.
Custom models, shipped products, or embedded integrations — our engineering team delivers machine intelligence that produces measurable business outcomes.
Custom AI Models
Domain-specific pipelines, fine-tuned LLMs for enterprise workflows, and production-grade inference that scales.
Cybersecurity Products
End-to-end product engineering — concept to deployment. We build the cyber tools that don’t exist yet.
Enterprise Integration
Drop AI into your existing SIEM, SOAR, and data stack without rip-and-replace.
Accredited in Oman. Certified globally.
Accredited cybersecurity provider — Sultanate of Oman.
Information security management system — global standard.














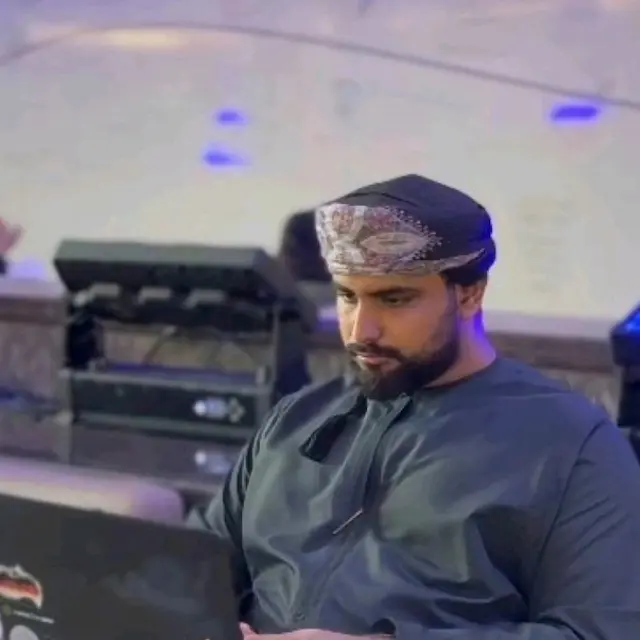
The operators
behind the signals.
Red team, exploit development, digital forensics, and threat-intel operators — with experience across telecom, banking, government, and blockchain.
Don't wait for
the next breach.
Book a 30-minute walkthrough. See live intel against your own domain, executives, and sector — in your first call.